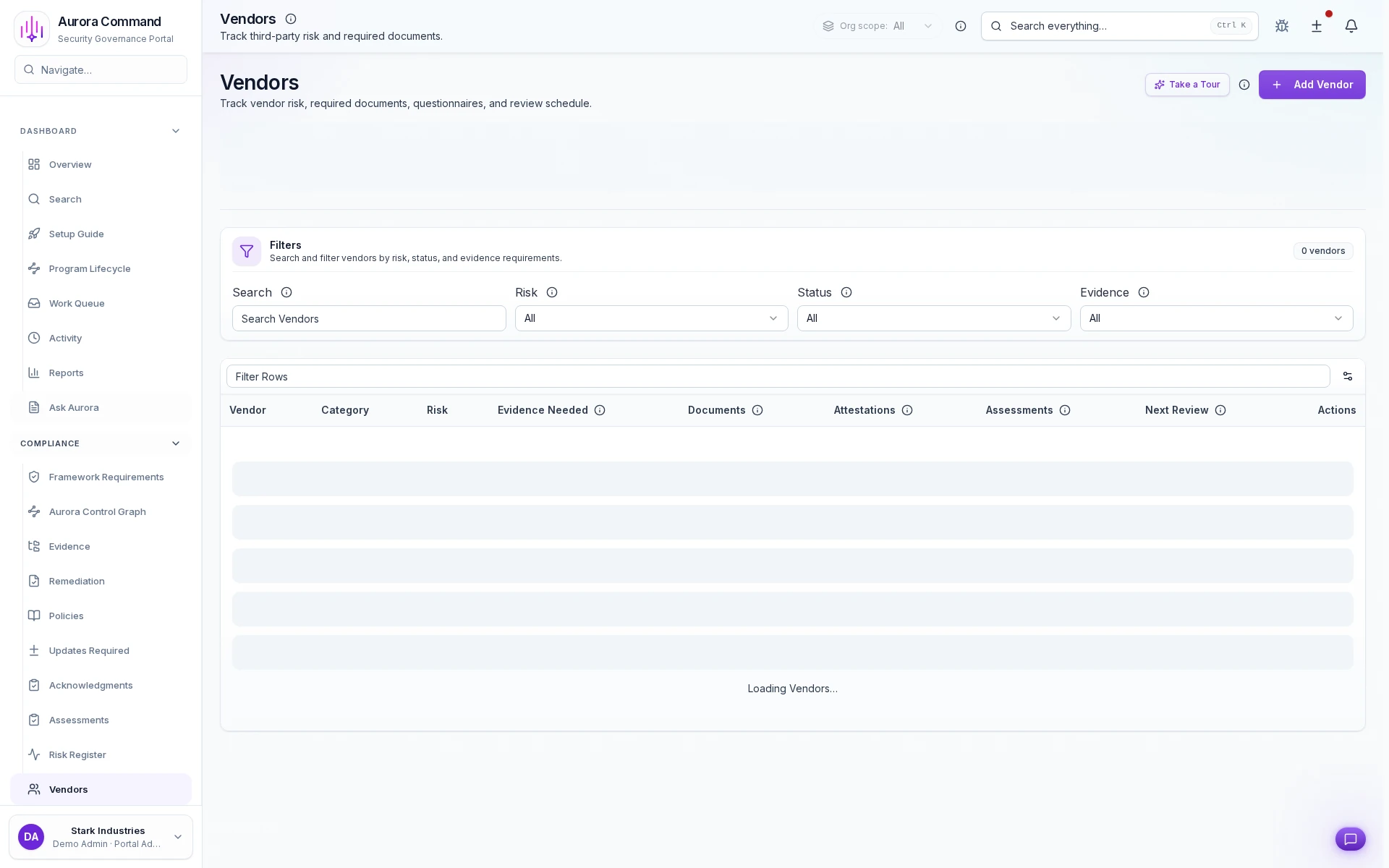
Run Vendor Reviews on a Governed, Repeatable Cadence
See how third-party reviews follow a governed cadence from onboarding through reassessment.
What you'll see
See the exact workflow, the proof that stays attached, and the control points that keep reviews from turning back into document chasing.
What you can verify in this walkthrough
You are seeing the live workflow, the attached proof trail, and the control points that matter once reviewers ask follow-up questions.
Structured vendor intake
New vendors enter a governed onboarding path with risk tier assignment, questionnaire dispatch, and due diligence tracking.
Questionnaire cycles stay on track
Reassessment cadences trigger automatically. Overdue vendors surface before gaps become audit findings.
Exposure tracking stays current
Risk exposure updates as questionnaire responses and due diligence artifacts arrive, keeping the vendor risk picture current.
Why this workflow matters
Third-party risk reviews stall without a governed cadence. When due diligence, questionnaires, and exposure tracking follow a repeatable process, nothing falls through procurement cycles.
Tell us about one vendor due for reassessment
In the live walkthrough, we show the intake path, questionnaire cycle, and how risk exposure stays visible.
Stop Resetting Vendor Reviews Every Cycle
Questionnaire history, tier-based scoring, and reassessment cadence that persist across review cycles.
Where This Fits
See how this walkthrough connects to broader workflows
- Identify and score organizational risks
- Evaluate third-party risk
- Monitor control drift continuously
What Most Teams Open Next
Most teams follow this walkthrough with the next proof flow they need to tighten, whether that is evidence collection, reviewer sharing, or readiness follow-through.
Vendor Questionnaire Reassessment
See how vendor reviews are reopened, reassessed, and closed with owners and renewal dates attached.
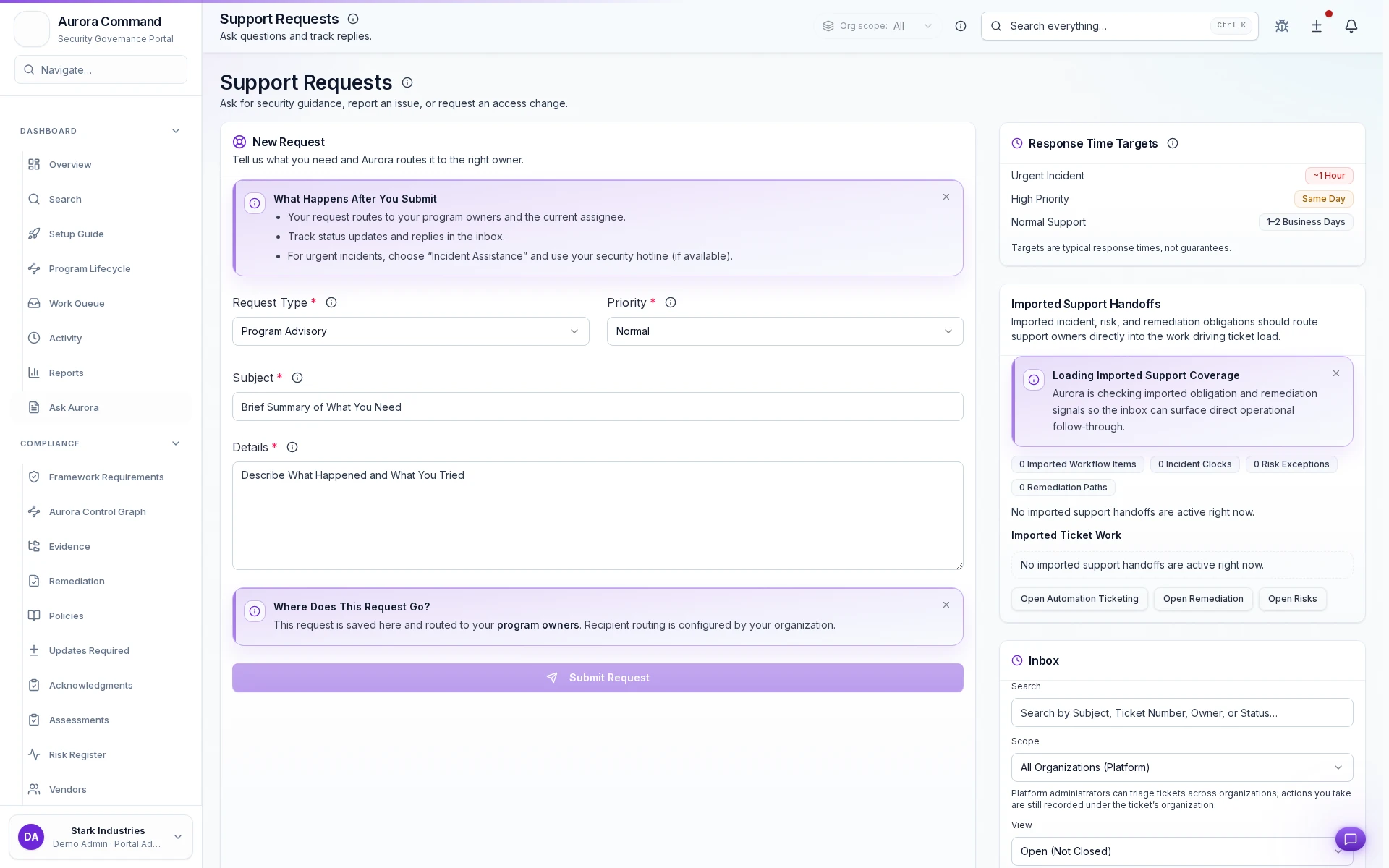
Support Requests
See how requests are triaged, assigned, and resolved with a defensible ownership trail.
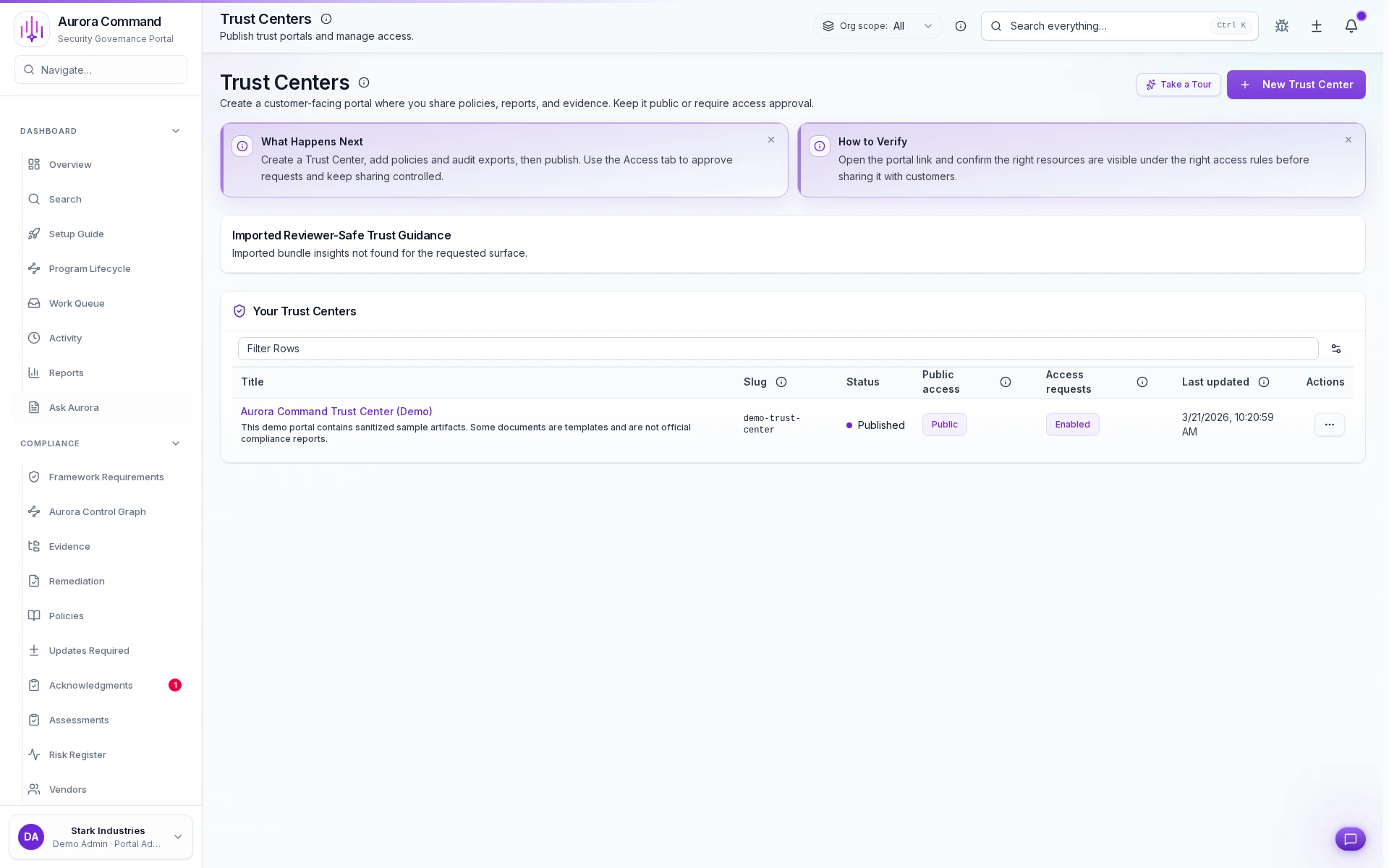
Trust Center
See how reviewers get scoped access to trust artifacts with tiered permissions and expiring links.