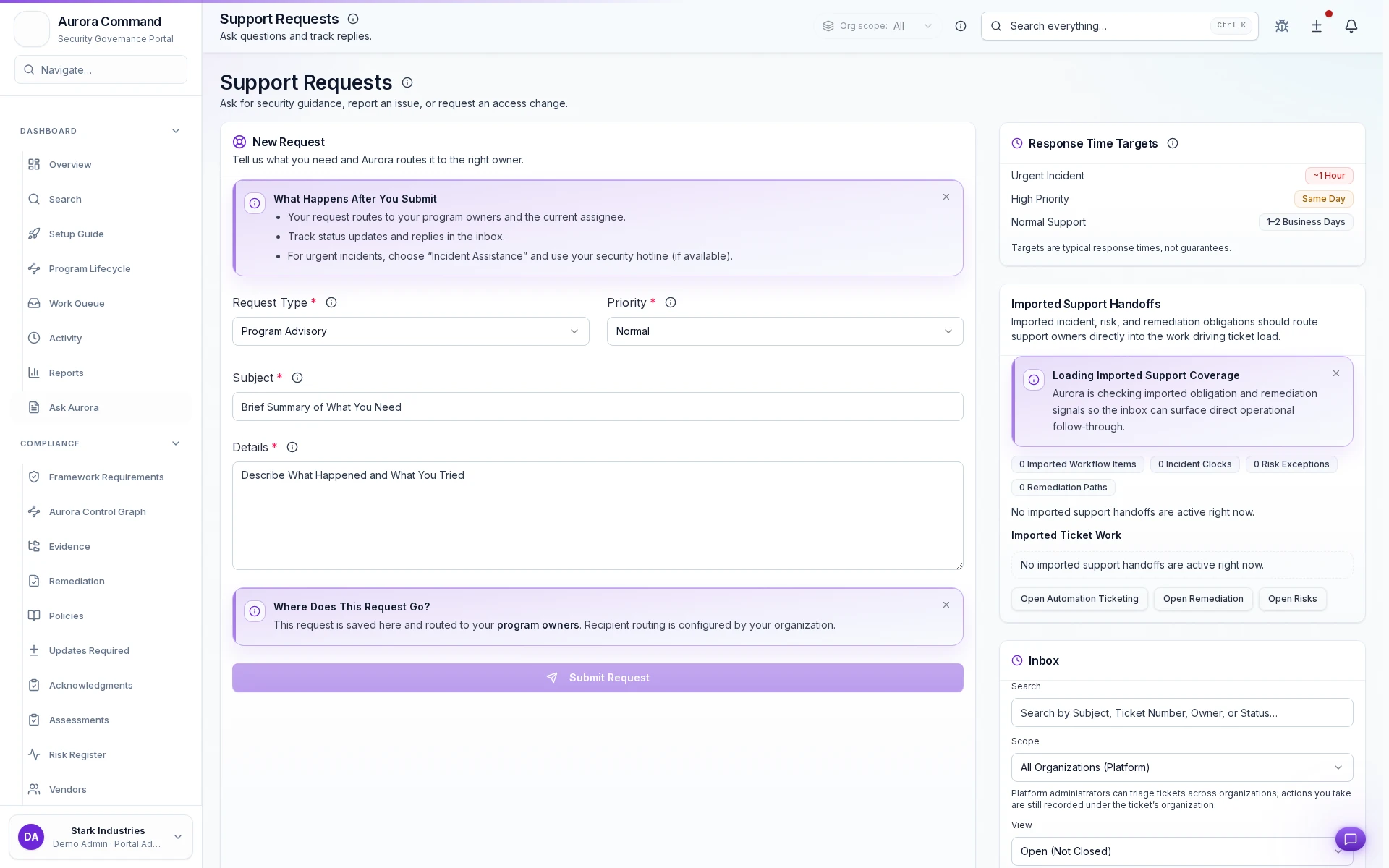
Resolve Requests With a Defensible Audit Trail
See how requests are triaged, assigned, and resolved with a defensible ownership trail.
What you'll see
See the exact workflow, the proof that stays attached, and the control points that keep reviews from turning back into document chasing.
What you can verify in this walkthrough
You are seeing the live workflow, the attached proof trail, and the control points that matter once reviewers ask follow-up questions.
Single-queue intake
Every request enters one governed queue with ownership assignment, priority, and category from submission.
Resolution history is defensible
Actions, status changes, and communications stay attached to the request record for post-incident review.
SLA visibility prevents drift
Response and resolution timers are visible to owners and managers so breaches are caught before they compound.
Why this workflow matters
Request operations lose accountability in shared channels. When intake, ownership, and resolution history live in one queue, teams can defend every outcome.
Tell us about one open request
In the live walkthrough, we show intake, triage, and how request history stays defensible.
Request History That's Defensible Under Review
Request intake, ownership routing, and response history that's defensible under review.
What Most Teams Open Next
Most teams follow this walkthrough with the next proof flow they need to tighten, whether that is evidence collection, reviewer sharing, or readiness follow-through.
Status & Ownership Audit Trail
Track every status change and ownership transfer with a complete audit trail.
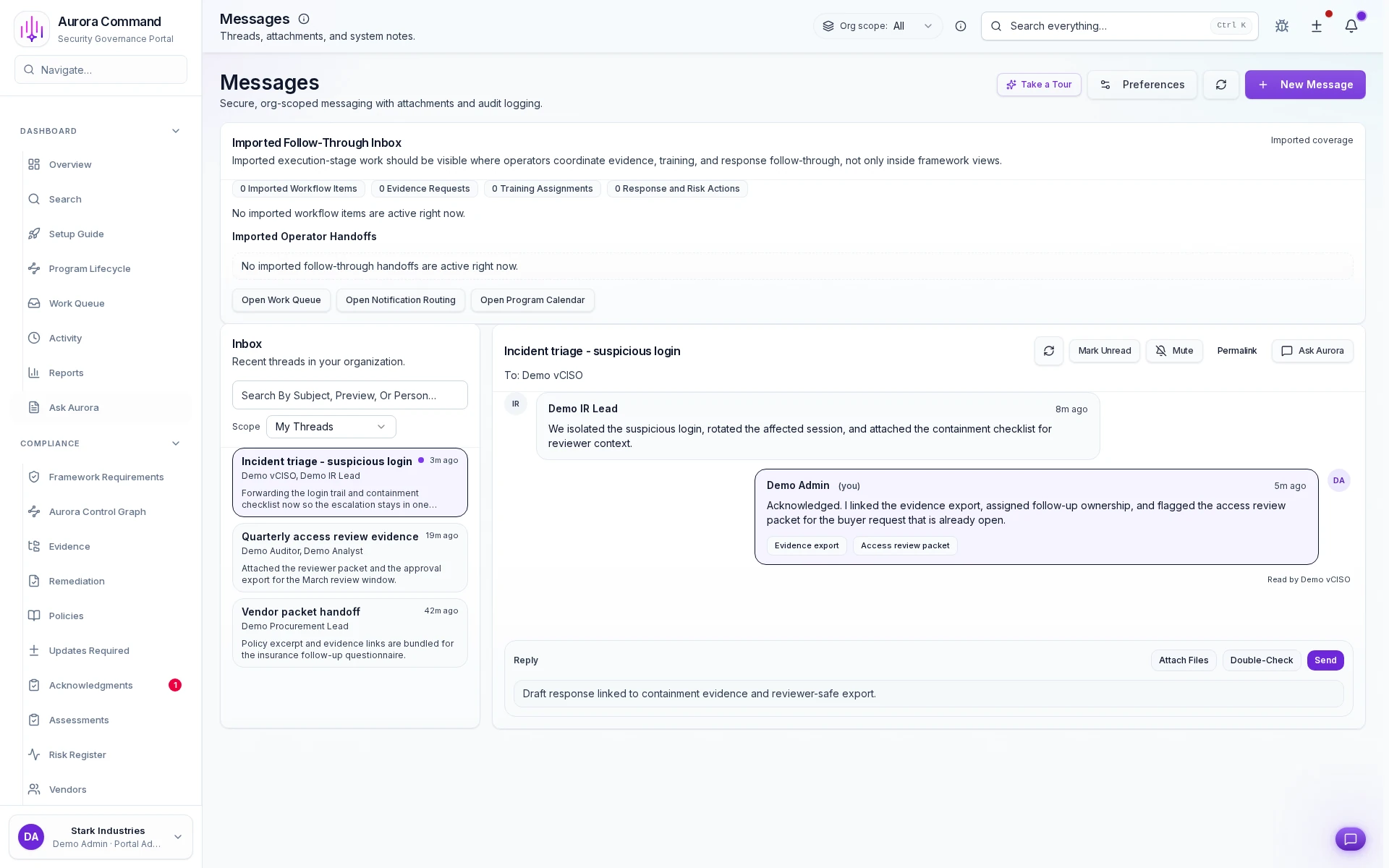
Messaging Operations
See how high-accountability communications are launched, acknowledged, and documented from one timeline.
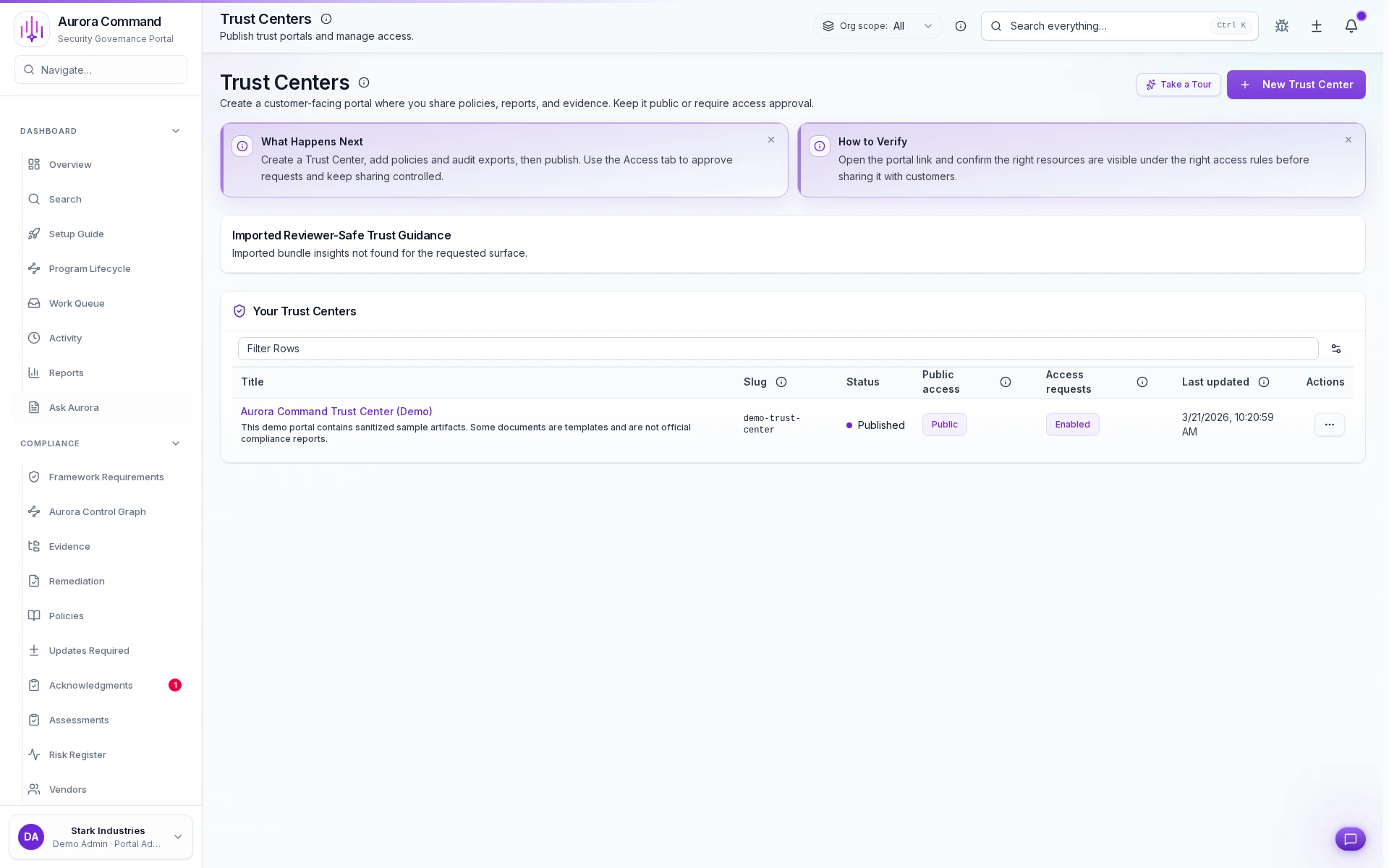
Trust Center
See how reviewers get scoped access to trust artifacts with tiered permissions and expiring links.