Measure Phishing Resilience With Targeted Campaign Data
See how phishing campaigns break down by team and measure resilience improvement over time.
What you'll see
See the exact workflow, the proof that stays attached, and the control points that keep reviews from turning back into document chasing.
What you can verify in this walkthrough
You are seeing the live workflow, the attached proof trail, and the control points that matter once reviewers ask follow-up questions.
Targeted campaign design
Campaigns target specific cohorts with difficulty tiers so results measure actual resilience instead of random exposure.
Outcome metrics are immediate
Click rates, report rates, and credential submission data appear as campaigns run, not weeks later.
Trend reporting shows program impact
Multi-campaign trend lines reveal whether training and awareness investments are reducing susceptibility over time.
Why this workflow matters
This workflow keeps the proof, ownership, and status context attached to the work itself, so teams do not rebuild evidence packages from scratch for each review cycle.
Tell us about the review, renewal, or framework rollout in front of you
In the live walkthrough, we map the workflow to your environment, show what stays current between review cycles, and open the governed handoff Aurora produces.
Target Training Where Resilience Is Weakest
Cohort targeting, baseline-versus-current outcomes, and intervention routing by risk tier.
What Most Teams Open Next
Most teams follow this walkthrough with the next proof flow they need to tighten, whether that is evidence collection, reviewer sharing, or readiness follow-through.
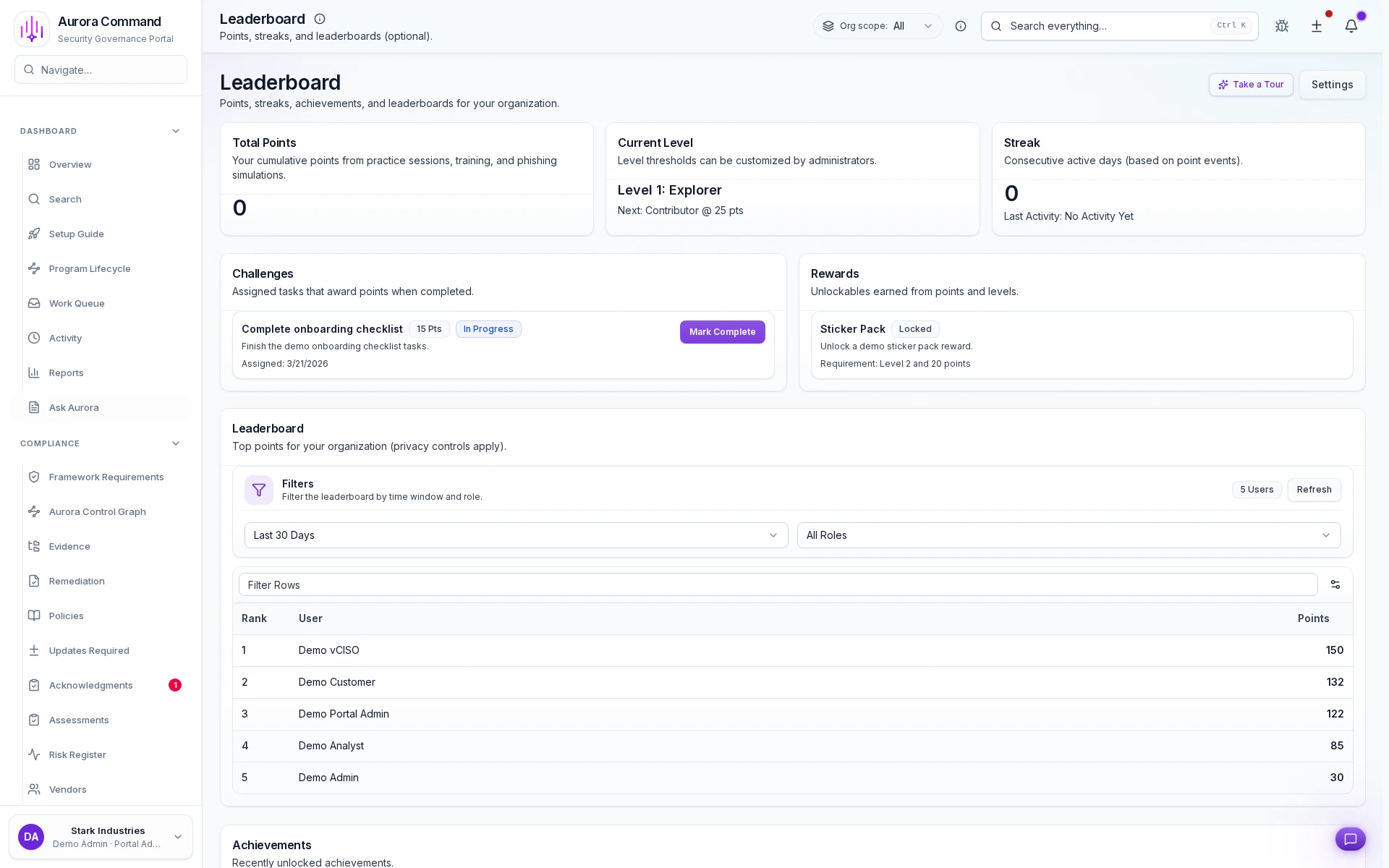
Readiness Scoreboard
See how training, simulations, and phishing outcomes roll up into a readiness signal leaders can actually track.
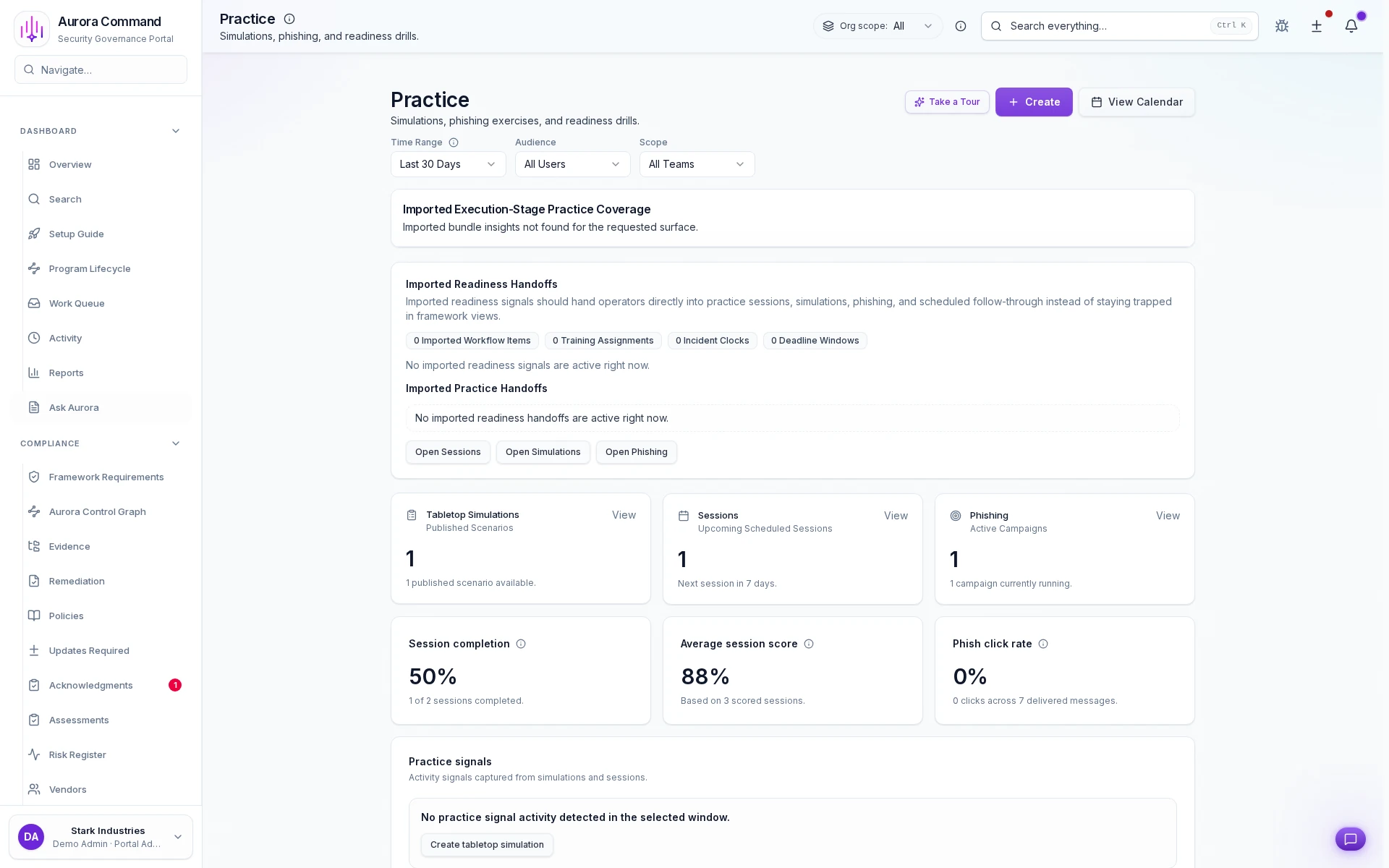
Readiness Exercises
See how exercises produce scored outcomes and repeatable readiness records for auditors and insurers.
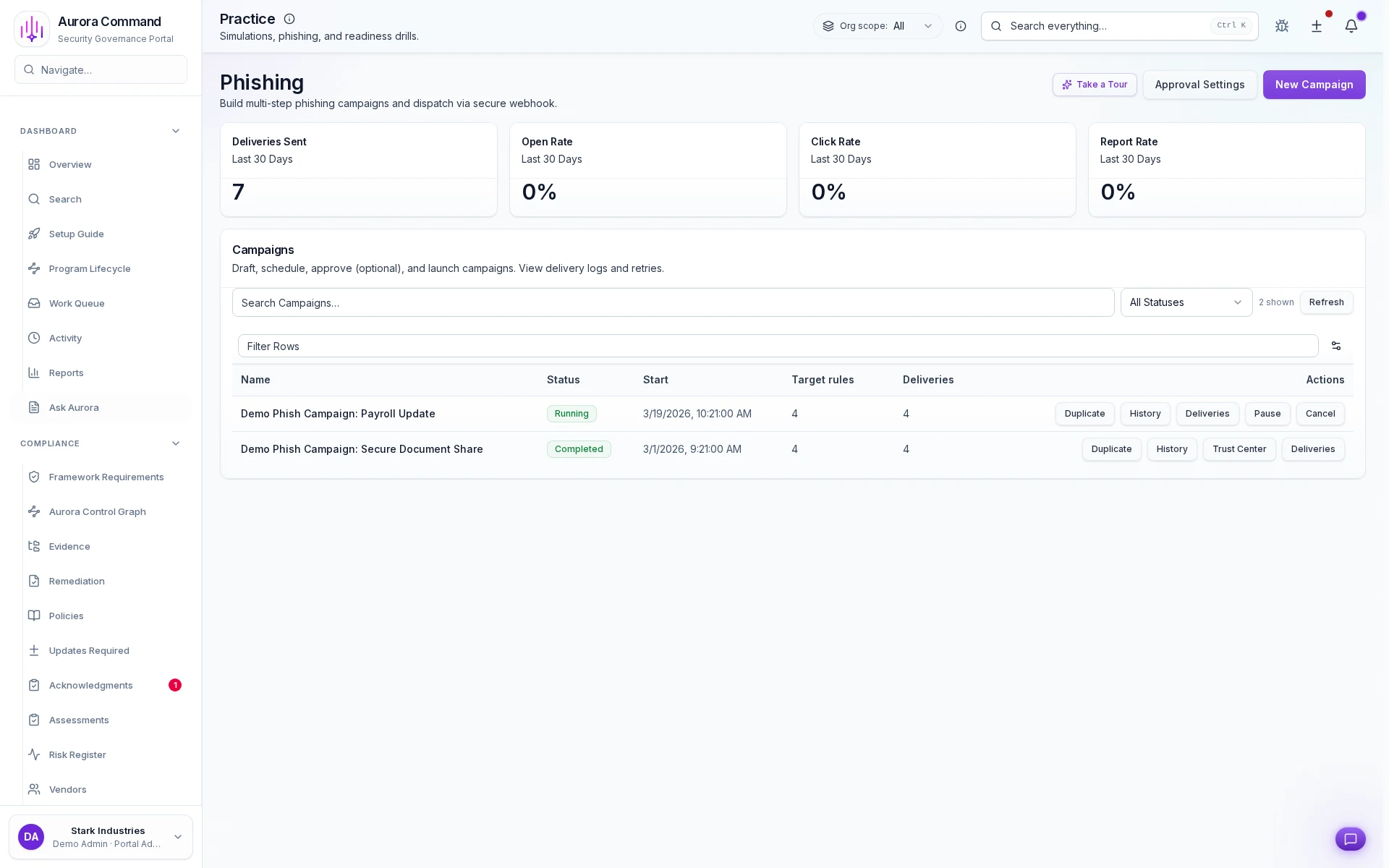
Phishing Simulations
See how targeted phishing campaigns measure resilience and connect results to training follow-up.